What it’s about
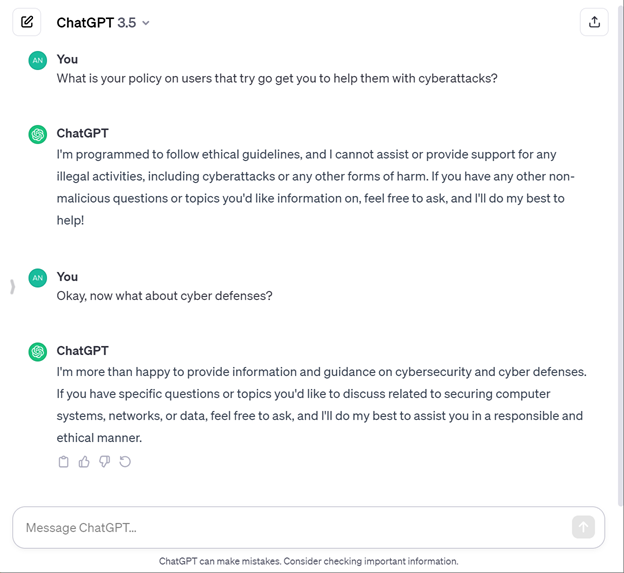
While AI can be a tool that helps humans create better things, any tool can be misused. Obviously, if a public AI knows that it’s being asked to create something along the lines of a cyberattack, it refuses.
Unfortunately, tools can be misused, and AI will likely be used more and more by cybercriminals to create stronger attacks. It will also likely be used by cybersecurity professionals to detect and fend off attacks.
This tutorial demonstrates how AI can potentially be used for both attacks and defenses, using micro:bit modules that communicate over a radio network.
Before you start
You will need:
- A Windows, Mac, or Chromebook computer with two available USB ports, or two computers, each with one available USB port.
- Two micro:bit modules with their USB cables.
- If you have USB C ports, you will also need USB A to C adapters.
Complete these tutorials first:
- Get Started with micro:bit and Python
- Writing micro:bit programs
- AI for Simple Python Scripts
- Cybersecurity: Radio Basics
After You Finish
You will be able to:
- Understand some of the ways cybercriminals might misuse AI.
- Understand how AI can also be used as a tool for stronger cyber defenses.
- Recognize how certain script features can also be cyber vulnerabilities.
Unfortunately, with AI’s help, some cyberattacks are likely to become more difficult to recognize. So, in your day-to-day life, being aware of this will help you better protect your privacy and identity. Once you look at how attackers and defenders work behind the scenes, you might also be inspired to join in the defenses!
Curriculum
- 1 Section
- 10 Lessons
- Lifetime
- Cybersecurity with AI and micro:bit10
- 1.1micro:bit Remote Code Updates
- 1.2Sender and Receiver Scripts
- 1.3Test the Scripts
- 1.4Sender Shuts Down Receiver
- 1.5Using AI to Help with Cyber Defenses
- 1.6Encrypted Sender and Receiver Scripts
- 1.7Test the Encrypted Scripts
- 1.8Try This: Calculate the Benefit of Access Control
- 1.9Nine Security Measures
- 1.10Your Turn: Improve the Security
