Imagine you are trying to open an old bike lock with 3 digits, each 0 to 9. That bike lock only has 1000 combinations (0 through 999). If it takes 3 seconds to test each combination, it would take 3000 seconds.
3000 seconds * (1 minute / 60 seconds) = 50 minutes.
In other words, your brute force attack would be guaranteed to succeed in just under an hour.
With four digits, the combinations increase to 10,000, and instead of 50 minutes, the same brute force attack could take up to 500 minutes.
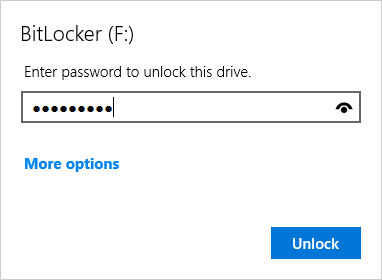
Computer passwords usually must be at least 8 characters, and use a variety of them — letters, upper-case, lower-case, digits, punctuation, and symbols like # $ %, etc. With 94 possible printable characters, how many different combinations would that be?
94 x 94 x 94 x 94 x 94 x 94 x 94 x 94 = 948 = 6,095,689,385,410,816.
A person could spend an entire lifetime manually testing passwords, and still not crack the combination! Even a computer trying 1,000,000 different combinations per second could still take up to 193 days to find the right one.
Did You Know? Machine Attack and Defense
Early examples of brute force attacks occured during WWII, when Allied Forces worked to crack ciphertext encrypted by German Enigma machines. These machines used a constantly shifting key from letter to letter. Due to the immense number of combinations, without a copy of the mechanisms that were being used, decryption by hand was impossible.
_-_Museo_scienza_e_tecnologia_Milano.jpg)
Museo della Scienza e della Tecnologia "Leonardo da Vinci" / CC BY-SA
A device known as the Bombe machine was invented to help crack the Enigma cipher. It systematically went through every combination of encrypted messages to reveal discernible original messages.

